There is a lot of talk about health and safety regulations in industry – it could be in the factories or smaller plants. Generally, wherever a person may be threatened by the slightest danger, there is a whole lot of regulations, security systems, protocols of proceedings, etc. Nobody is surprised. Human life is the most precious. However, very little is said about the security of data and ICT networks, which are, after all, increasingly used in automation. Nowadays, the goal is to fully automate processes, mobility of solutions, use of IT in automation systems, IoT and IIOT solutions, and many, many more.
Controlling smelting via an industrial tablet wirelessly!… Or a huge excavator that works several dozen kilometers away is no longer rocket science 😛 In the IT industry, engineers face the problems of securing networks and data against leaks or attacks from outside. But does that mean the problem is not with the automation industry?
Initially, the devices communicated on the internal network, whether via Modbus, Can, DeviceNet or Profibus, in the RS-232 or RS-485 standards, etc. In fact, it still is, and the protocols themselves in terms of security have not changed much since the 1970s. Access to such devices from the outside was practically impossible from outside the facility. The only threat was the interference of third parties into the internal corporate network only after the physical connection or neglect of employees. By the time…
Today, when we often use remote access and communication via the Internet, virtually every network device is exposed to attack. Unfortunately (and fortunately) today it is difficult to imagine the operation of industrial systems without the use of extensive ICT networks. Greater work efficiency, access to a much larger number of devices at the same time from one end point, which can be a maintenance worker, programmer, much faster failure resolution or even monitoring of performance parameters and device statuses. These are just a few advantages of industrial automation work in extensive ICT networks.
With great power comes great responsibility… 🙂
It is enough for the controller to be connected to a switch, switch to another switch, somewhere along the way there will be a Hub, maybe a media converter, one router, a server room, and finally an edge router and a public network. We can also communicate from the office or home with a PLC via a GSM modem .. (why not?).
Without a good security policy and a number of safeguards, our network will never be safe.
Threats
In 2010, a bug was detected in Iranian industrial systems (including Libya and Natanz) that infected PLC software. It was called Stuxnet. Another type of infecting software was used to ‘reconnoitre’ the area. Stuxnet checked and recognized whether Siemens devices (mainly S300 / S400, inverters and SCADA Siemens) were connected to the infected computer. As a result, it gradually changed the settings of the operating parameters of the centrifuges, which, over time, led to their damage. The bug was intelligent enough to put alarms and system notifications to sleep, making it almost invisible. Additionally, he periodically put himself to sleep, becoming even more undetectable. How did it get infected? Probably due to staff negligence, lack of security and routine…. What were the aftermath of Stuxnet? Sometimes there is talk of damage to Iran’s uranium enrichment plants and delays in the nuclear program itself. Engineers, unable to identify the problem, were often forced to replace sets of damaged devices.
Can you imagine the consequences of going crazy, virus-infected control of large industrial automation systems? The scenes might not be as epic as the machines riot in the Terminator series, but the damage could be serious.
In later years, several versions of malware also appeared, such as Flame, Gauss and Duqu. According to the latest data, there are tens of thousands of unauthorized access / intrusion to industrial process control systems each year. It is not uncommon that such attacks are detected very late or not at all. According to Cisco’s research, the average time to detect a security incident from its occurrence is … comments: 400 days!
CyberX [1] undertook an analysis of the security of industrial networks, which shows that:
- One-third of industrial plants are connected to the Internet -> which does not require additional explanation as to what easy targets such networks are;
- In 3 out of 4 industrial plants there are unsupported Windows operating systems, such as XP and 2000 -> such systems are no longer updated, no new security policies, so the system will no longer recognize new threats;
- Almost 3 out of 5 plants use unencrypted passwords in the form of plain text, allowing access and movement within the OT network -> it is not new, the access passwords are written with markers on the housing of devices or glued to sticky notes;
- Half of the industrial sites do not have any anti-virus protection;
- Almost half of the companies have at least one unknown or foreign device, and 20% have wireless access points (WAP) -> it is much easier to get to the wireless network;
- On average, nearly a third of the devices (28%) in each plant are susceptible;
- 82% of industrial sites use protocols for remote connection: RDP, VNC and SSH;
Protect and prevent
The basic way to fight attacks is to properly design the entire ICT network. Proper segmentation and network separation becomes the most important.
First, the network should be divided into subnets depending on the destination. An office network should be included in a separate group, an industrial network and a public network in another. Each of the superior groups should be divided into appropriate departments of our plant, which in turn into subnets depending on the type of devices. Example: PLC controllers should be in a different network than even VoIP.
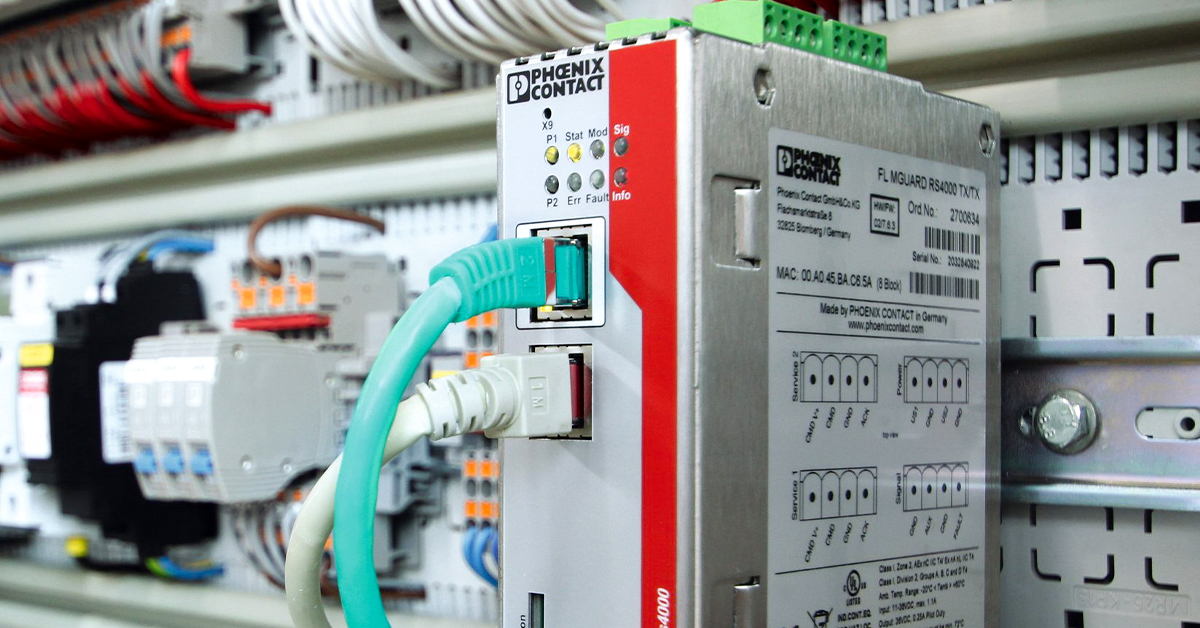
Additionally, it is necessary to use devices with built-in firewalls. An important element of network separation is its division into VLANs. This allows the different segments to be logically separated in the third TCP tier of the OSI model. Inbound and outbound traffic should be controlled through ACLs defined at the device level. The best solution to ensure a strong firewall, in addition to setting it on individual devices, is to connect to the network a separate device that supervises traffic and security, which are Firewall or UTM servers. The latter are very helpful firewalls housed in a single switch-like device. It is also possible to set a firewall on the application layer of the OSI model, which some may consider an exaggeration in industrial networks, but it should also be mentioned.
A good, and perhaps the most logical, security practice is to disconnect devices that simply don’t need them from the Internet. For example, operators should only have access to the industrial network segment in which the PLC communicating with the HMI operates, so that employees have access to the control and process parameters, and not to the latest season of Game of Thrones: D.
The entire network should be carefully monitored. It is very easy to obtain data with too much authorization, therefore, trained and competent persons with exclusive rights, also protected against third parties, should be appointed for the administration of resources and taking care of the ICT network. I have often encountered a situation where, after connecting to the client’s network via VPN, my computer was scanned by antivirus and had to meet some kind of security standards (including the current operating system, active firewall, legal software, etc.). Personally, it was very irritating, but in fact, it made it a lot safer.
When it comes to remote and VPN connections, it is even necessary to use transmission encryption protocols, the well-known PKI credentials system and other security certificates. Moreover, all certificates should be up-to-date and periodically renewed. It is very important that the private keys of each user are stored on media inaccessible to third parties and protected with additional security.
What about new devices?
Our network administrators should be in control of all devices on the network. Other employees or contractors wishing to connect new devices to the network or obtain IP addresses should be properly trained, the entire history of changes and accesses should be saved and stored in the system, and the devices should be thoroughly checked for security and compliance.
Lawlessness is not an option!
Another issue is probably data transfer, saving passwords. It is necessary to use encrypted transmission of sensitive data, ie passwords, device configurations, etc. It must not be possible for situations in which the password is sent by e-mail or written on a piece of paper and “passed on” (known practice).
The most ad hoc method of protection is to physically secure the devices and infrastructure themselves. I mean the control and security of control cabinets, rooms, server rooms and access passwords or data warehouses in the form of:
- RFID readers and cards,
- using hard-to-break passwords refreshed periodically,
- mechanical security of devices and rooms (padlocks, electronic locks, etc.),
- increased control of authorized persons – I mean the principle of limited trust. More than once I had the opportunity to have access to everything on the site and do whatever I want with the networks, because no one was interested in what I am actually doing here,
- training for staff to raise awareness of safety,
- performing security audits.
SUMMARY
As you can see, security in industrial networks is very important and, according to many, more important than in IT networks. As the owner of an industrial plant, it is worth considering how to improve the security of your network. As is known, prevention is better than cure. It is worth considering training for employees, security audits, introducing internal protocols and security policies. It becomes practically necessary to expand the IT department of your own company with a security department. This will allow to detect and prevent attacks on our network in a very short time and, consequently, save time, work and stress on repairing failures and possible line stops.