The virtual world has become as important as the real one. It is especially visible now – as the world is struggling with the coronavirus and everyone is moving online. Certainly, a large number of automation specialists now perform their duties remotely, as I do. By connecting, developing and carrying out operations on important company resources.
At the same time, the cybercrime risk related to data theft has increased rapidly in recent times, raising awareness of VPNs as a way to effectively improve our privacy.
This article was written after my recent training about “Online Safety.” We will take into account the most important factors that should be taken into account when choosing the best VPN for a small and medium-sized company where automation specialists usually work. At the beginning let’s start with the concept of a VPN.
What is Virtual Private Network (VPN)
Virtual Private Network (VPN) is best illustrated in the picture below:
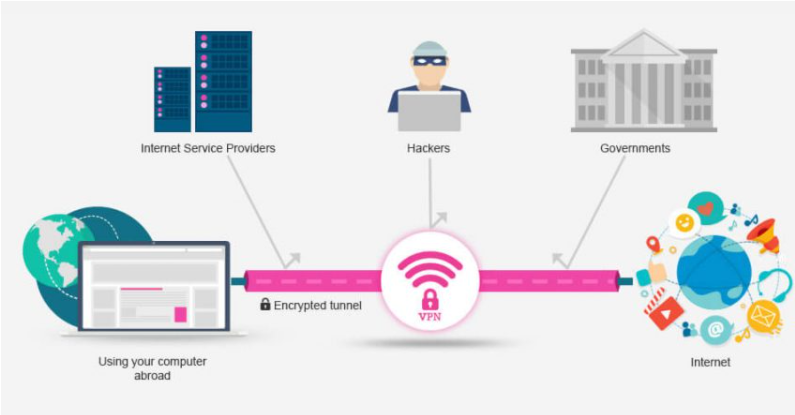
A VPN is a service that creates an encrypted connection from your device to a VPN server through your internet connection. Think of it as a tunnel through the mountain where your Internet Service Provider (ISP) is the mountain, the tunnel is a VPN connection, and the exit is available to the world wide web.
There are a few people who can confuse VPNs as an alternative to an Internet connection, but this is incorrect.
Originally, VPNs were created to connect business networks for safer and more convenient communication. Currently, VPN service providers are working hard to forward all traffic to the internet – in some cases bypassing government or ISP monitoring or even forced censorship.
In short, think of a VPN as a service that aims to help you get full internet access and keep you safe during this time.
VPN in a business
A frequent use of a VPN is the ability to connect to the company’s resources by an employee who is currently outside the workplace. This allows, for example, to work remotely or to connect a person on vacation to the corporate network. In addition, larger companies that have, for example, several branches in different cities can increase the security of communication between them.
Another business use is to set up an encrypted tunnel between the client and the company providing services to him. A VPN enables a secure connection, and thus increases the quality of services provided. This increases the level of confidence and trust in the customer who, for example, transfers confidential data to an external company. In the case of private use of a VPN, the user may want to increase e.g. the security of the connection. This applies if you are trying to connect to a public WiFi network, such as in a coffee shop or airport.

A VPN also works when we want to bypass a regional block. For example, by wanting to access a service available only to users located in the United States, the user, through the American VPN server, can bypass the blockade.
A VPN also works when a user is actively sharing or downloading data from the internet and wants to increase their anonymity. This way, if our communication is encrypted, the ISP will not be able to observe what data is shared or downloaded.
The choice of a VPN – the most important factors
- Encryption – Various versions of data encryption and multiple security protocols are available.
- Server network – the more extensive and the more servers, the better.
- Speed and type of allowed traffic – when downloading or sharing files, it is worth checking what restrictions are introduced by the provider.
- Country of origin of the owner of the VPN service (and what law it is subject to) – of course, this includes China and Russia
Why is China a bad choice?
By law, ISPs in China must provide all information about their customers and their data when requested by the authorities. It is similar in Russia. But it’s not just these two authoritarian countries that are a bad choice when it comes to VPNs.
To the countries “spying” Internet users should add the so-called “14-eyes countries”, i.e. a coalition of countries that monitor (read: surveillance) telecommunications networks on a mass scale and exchange data with each other (read information about your internet traffic and can access them):
- USA (5 companies from this country control 32 brands of VPNs)
- Australia
- Canada
- New Zealand
- United Kingdom
- Denmark
- France
- The Netherlands
- Norway
- Germany
- Belgium
- Italy
- Sweden
- Spain
- … and additionally Switzerland, Israel, Signapur, South Korea and Japan, which are not officially in the “eye coalition”, but strongly sympathize with the US.
3 top choices for automation specialist
Now that we’ve covered how a VPN works and what are the most important factors when choosing a provider, I will present the top 3 VPN solutions available for individuals and small businesses.
1 Nord VPN
Benefits:

- “The cheapest of the best and the best of the cheapest” according to the portal Bezpiecznik.pl
- VPN configuration on up to 6 devices
- a residence in Panama, the political system of which makes it impossible for someone to reach for certain companies
- 0 log policy (does not log internet traffic that passes through their servers)
- the ability to pass traffic through the Tor network
- 5674 servers worldwide
- works on any operating system
- allows and does not ban for torrenting
Disadvantages: no support 24 hours
Price:
- Basic: $ 11.95 / month
- Normal: $ 5.75 / month
- Best deal found: $ 3.29 / month
2 Express VPN

Benefits:
- Reliable and very fast speed on all servers
- Zero logs
- 24/7 online support
Disadvantages:
- Relatively expensive compared to competitors
- Untagged streaming servers
- Disconnects from time to time
Price:
- Monthly Package: $ 12.95 / month
- 6 months package: $ 9.99 / month
3 IPVanish

Benefits:
- Relatively inexpensive compared to Express VPN
- Unlimited bandwidth and speed
- P2P file sharing
- 24/7 support
- Money back guarantee (within 7 days)
- Various protocols for added security
- A reliable encryption method
- Effective bypassing region blocked sites
- Zero logs
Disadvantages: no free trial
Price:
- Annual package: $ 6.66 / month
- 3 months package: $ 8.99 / month
- Monthly Package: $ 10 / month
Choosing the best VPN for automation specialist
Based on various tests found on the internet, it’s fair to say that NordVPN is the most comprehensive solution on the market today. We can unblock different sites blocked in a given region quite easily and download files quickly and securely from various resources (including your company’s cloud).
That being said, NordVPN is very safe to use abroad, whether or not you’re using unsecured public Wi-Fi connections. It is also not without significance that his residence is located in Panama, the political system of which makes it impossible for someone to reach for data.
A solution dedicated to the industry
Moxa Remote Connect – Manage your remote access in the cloud
Remote access to controllers and machines is essential nowadays and allows you to add value to the customer and avoid unplanned downtime. For example, when a manufacturer of industrial compressors is able to remotely monitor the status of a machine, change settings, predict wear of parts, it can anticipate possible failures and thus schedule a service. Moxa offers an intuitive remote access solution called MRC (Moxa Remote Connect). The solution consists of 3 components: MRC server hosted by the manufacturer or maintained in-house; MRC gateway purchased from the manufacturer and MRC client, i.e. a Windows application for establishing a connection. MRC Server can be deployed in 2 ways:
- Purchase of a license for the MRC server and run it on your own virtual machine in AWS.
- Register the purchased MRC gateway and use the free Moxy server – MRC Quick Link
The first approach is quite innovative as the user becomes vendor independent and is responsible for maintaining the server on Amazon Web Services. This involves purchasing a server license and machine maintenance fees, but you gain independence and control and do not share the server with other companies. The second solution is the most popular on the market and allows you to quickly and easily connect up to 5 nodes to the Moxy MRC Quick Link server.
Summary
With the steady increase in online services and cybercrime, VPN seems to be one of the tools that can increase the level of user security. However, keep in mind that we are never 100% safe. This article is based on a variety of information available on the Internet.
